OPSEC used to mean hiding your secrets from smart men. Mythos means hiding is no longer enough, because now even a fool can rent a genius by the token. --YNOT!
What happens to operational security when the adversary no longer needs to be a genius, only awake?
That is the question sitting underneath all the noise around Mythos. Anthropic did not introduce Mythos like a shiny new app or a faster chatbot. It introduced Claude Mythos Preview through Project Glasswing as a restricted, defensive-security effort, saying the model is a general-purpose frontier system that can surpass all but the most skilled humans at finding and exploiting software vulnerabilities. Anthropic also says it has already found thousands of high-severity vulnerabilities, including flaws in every major operating system and web browser.
Traditional OPSEC—operations security—was built on a simple and honest principle: do not hand the enemy the puzzle pieces. The term grew out of the Vietnam era, after the military realized adversaries were assembling seemingly harmless scraps of information into a useful picture. The modern definition is still plain enough for common folk: identify critical information, protect it, reduce vulnerabilities, and deny the adversary easy understanding of your intentions and capabilities. In other words, old OPSEC assumed the enemy had to work for his supper.
Mythos changes that assumption because it does not merely “know about cyber.” It appears to reason through codebases, hunt for zero-days, reverse engineer exploits, and chain vulnerabilities together with the patience of a senior engineer and the stamina of a machine that never gets bored. Anthropic’s technical write-up says Mythos identified and exploited zero-day vulnerabilities in every major operating system and every major web browser during testing, and that it found several thousand more high- and critical-severity vulnerabilities now going through responsible disclosure. The UK AI Security Institute reported Mythos succeeded on expert-level capture-the-flag tasks 73% of the time and became the first model they tested to complete a 32-step corporate network attack simulation end to end, though they also cautioned that the environment lacked active defenders and does not prove autonomous success against well-defended real-world systems.
That is why Mythos was restricted. Anthropic says outright that Mythos Preview is not being made generally available, and AWS describes it as a gated research preview. Project Glasswing gives access first to major defenders and critical-software organizations so they can scan and harden the foundations before every crook with a Wi-Fi signal gets the same horsepower. Anthropic says the fallout from uncontrolled proliferation could be severe for economies, public safety, and national security, and it says its eventual goal is not permanent lockdown but a safer broad release of Mythos-class models after stronger safeguards are tested on less risky systems like Opus 4.7. That matches the central argument in the text you shared: this was treated less like a product launch and more like a fire drill with lawyers.
So, is Mythos the end of OPSEC? No. It is the end of lazy OPSEC. It is the end of the old comforting fiction that security mainly means hiding diagrams, restricting memos, and hoping the attacker is slower, dumber, or less caffeinated than you are. The text you shared puts that plainly: the real danger is not that AI becomes evil, but that offense starts moving at machine speed while defense still moves at corporate speed. When that happens, the “boring” disciplines suddenly become the crown jewels—asset inventory, patch discipline, logging, least privilege, dependency hygiene, supply-chain security, and faster update cycles. Anthropic’s own guidance says patch cycles must shrink because turning public CVEs into working exploits can now happen much faster, cheaper, and with far less skill than before.
What the future holds is both impressive and unnerving. The UK government, citing AISI’s work, warned this week that frontier-model cyber capabilities are now accelerating faster than previously expected, with capabilities doubling roughly every four months rather than every eight. That does not mean every teenager with a gaming PC becomes a master intruder tomorrow. It does mean the skill floor drops, the speed of exploit development rises, and the advantage tilts toward organizations that can detect, validate, isolate, and patch faster than the next man can improvise a proof-of-concept. It also means concentrated access becomes its own political problem, because whoever controls tools like this controls not just productivity, but the tempo of defense and offense alike.
The strange little moral here is that Mythos does not kill OPSEC. It exposes what OPSEC was always supposed to become. In the old world, good security meant keeping secrets. In the new one, good security means assuming the secret is already halfway out the door and building systems that can survive that fact. The real question is no longer, “Can we hide our weaknesses?” It is, “Can we fix them before the machine on the other side notices them too?”
And that is a rougher world, but maybe a more honest one. A lock was once judged by whether a thief could pick it. Soon it may be judged by whether it can survive being studied by a million sleepless minds at once.
What Are the 10 Rules of OPSEC in 2026?
- Trust nothing just because it lives “inside.”
In 2026, the old castle-wall model is tired, overweight, and lying to you. Zero trust means no implicit trust based on network location or ownership; verify users, devices, and sessions every time. (NIST Computer Security Resource Center) - Know what you own, or prepare to lose it.
Assets, identities, software components, cloud services, secrets, and dependencies all count. If you cannot name the resource, you cannot protect the resource. NIST’s whole point is that modern security protects resources, not just segments of a network. (NIST Computer Security Resource Center) - Patch like the enemy already has the exploit.
Because he may. Anthropic’s Glasswing partners describe a world where the window from discovery to exploitation has collapsed, and the UK’s NCSC warns AI will make it easier, faster, and cheaper to discover and exploit weaknesses. (Anthropic) - Least privilege is no longer optional manners; it is survival.
Give people, services, and machines only the access they need, and no more. When compromise comes, you want a cut finger, not an arterial bleed. (NIST Computer Security Resource Center) - MFA everywhere. Phishing-resistant MFA where it matters most.
A password by itself is just a polite suggestion. CISA says MFA should be standard, and phishing-resistant methods such as FIDO/WebAuthn are the bar organizations should be moving toward. (CISA) - If it is not logged, it did not happen in any useful sense.
In a breach, memory turns to pudding and opinions multiply like flies. Good logging, audit trails, and retained evidence are what let you detect intrusions and prove what happened. (CISA) - Treat vendors and open source like family at Thanksgiving: love them, but count the silver afterward.
Third-party software is now part of your attack surface. CISA’s SBOM guidance exists for exactly this reason: modern software depends on outside components, and you need transparency into those ingredients to manage supply-chain risk. (CISA) - Use AI on your own systems before someone else uses AI on them for you.
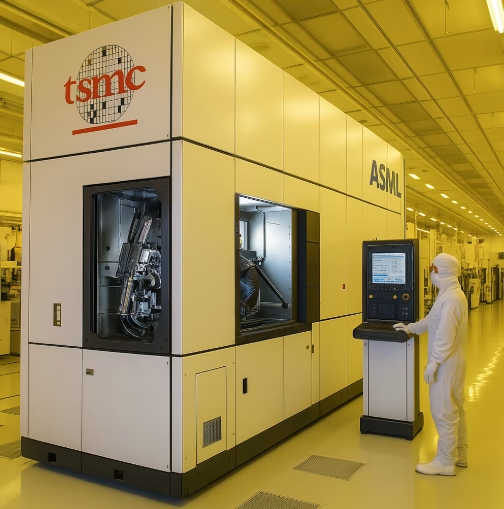
Mythos was restricted precisely because frontier models can find and help fix vulnerabilities at pace and scale that were previously impossible. The lesson is plain: defenders need AI-assisted review, testing, and hardening now, not after the first ugly surprise. (Anthropic) - Stop buying software that charges extra for basic safety.
Security features should not be luxury trim on the deluxe package. CISA’s secure-by-design position is that MFA, logging, and SSO should be available out of the box and not hidden behind a toll booth. (CISA) - Have an incident response path before the incident picks one for you.
Know who decides, who isolates, who communicates, who reports, and who restores. In a real event, confusion is the attacker’s favorite accomplice. (CISA)
OPSEC in 2026 means assuming the attacker has AI, speed, scale, and patience—so your defenses must have discipline, visibility, and fewer places to hide your own foolishness.
#Mythos #OPSEC #CyberSecurity #Anthropic #ProjectGlasswing #AIsecurity #ZeroDay #SecureByDesign
© 2025 insearchofyourpassions.com - Some Rights Reserve - This website and its content are the property of YNOT. This work is licensed under a Creative Commons Attribution 4.0 International License. You are free to share and adapt the material for any purpose, even commercially, as long as you give appropriate credit, provide a link to the license, and indicate if changes were made.